Cybersecurity threats continue evolving, making awareness and testing essential for individuals, organizations, and security professionals. Zphisher, known as an open-source phishing simulation toolkit, plays a role in ethical security testing when used responsibly. This guide explains Zphisher in a safe, legal, and educational context, focusing on awareness, controlled testing, and best cybersecurity practices.
What Is Zphisher?
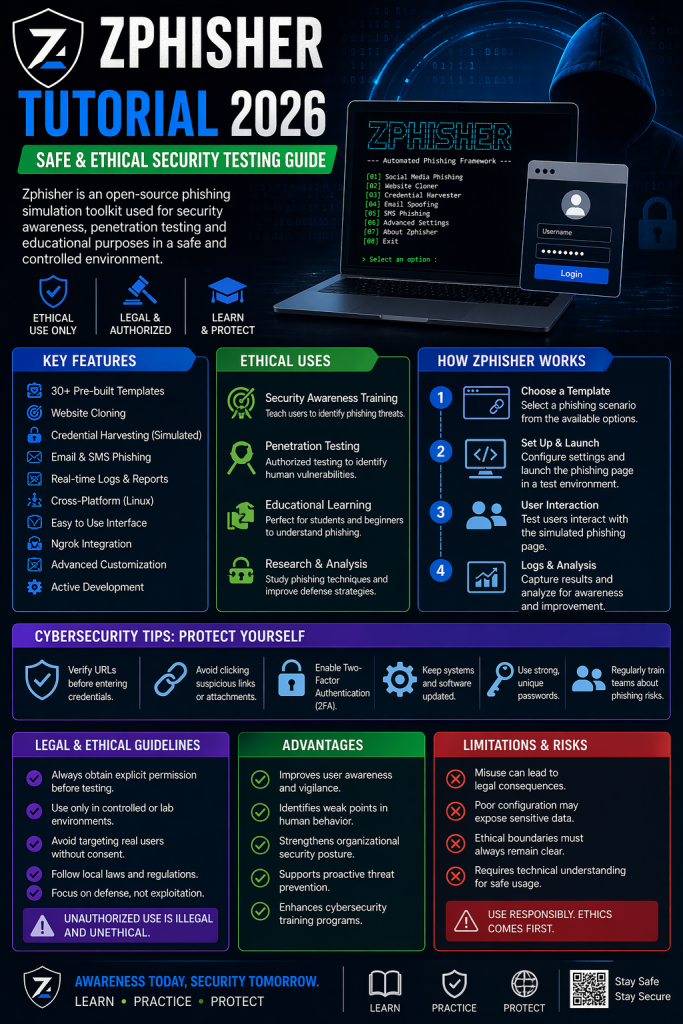
Zphisher functions as a phishing simulation framework designed for security research and training purposes. It helps cybersecurity learners understand how phishing attacks operate, enabling them to recognize vulnerabilities and improve defenses.
Instead of harmful use, Zphisher should remain limited to:
- Controlled lab environments
- Authorized penetration testing
- Cybersecurity education programs
Unauthorized use against real targets without permission remains illegal and unethical.
Key Features of Zphisher
Zphisher provides several capabilities that make it useful for learning and testing:
- Pre-built templates for phishing simulations
- Website cloning concepts for awareness training
- Credential capture simulation (educational context only)
- Cross-platform compatibility (Linux-based systems)
- Integration support for testing environments
- Real-time logs for analysis and reporting
These features help learners understand attacker techniques while focusing on defense strategies.
Ethical Uses in Cybersecurity
Zphisher supports multiple legitimate use cases when handled responsibly:
Security Awareness Training
Organizations simulate phishing scenarios to train employees in identifying suspicious links, emails, and login pages.
Penetration Testing (Authorized Only)
Security professionals use controlled phishing simulations to evaluate human vulnerabilities within systems.
Educational Learning
Students and beginners explore phishing mechanisms in safe lab environments to strengthen cybersecurity knowledge.
Research and Analysis
Researchers analyze phishing trends, behavior patterns, and prevention techniques.
How Zphisher Works (Conceptual Overview)
Zphisher demonstrates phishing workflow in a simplified educational model:
- Selection of a simulated scenario
- Creation of a test phishing interface (lab environment)
- Controlled interaction with test users
- Collection of results for awareness analysis
This process helps identify weaknesses without causing harm.
Cybersecurity Tips for Protection
Understanding phishing tools should always lead to stronger defenses. Follow these best practices:
- Verify website URLs before entering credentials
- Avoid clicking unknown or suspicious links
- Enable two-factor authentication (2FA)
- Keep software and systems updated
- Use strong, unique passwords
- Educate teams about phishing risks regularly
Awareness remains the strongest defense against phishing attacks.
Legal and Ethical Guidelines
Using tools like Zphisher requires strict adherence to ethical standards:
- Always obtain explicit permission before testing
- Use only in controlled or lab environments
- Avoid targeting real users without consent
- Follow local cybersecurity laws and regulations
- Focus on defense, not exploitation
Ignoring these guidelines can lead to legal consequences.
Advantages of Ethical Phishing Simulation
- Improves user awareness and vigilance
- Identifies weak points in human behavior
- Strengthens organizational security posture
- Supports proactive threat prevention
- Enhances cybersecurity training programs
Limitations and Risks
Even in ethical use, risks exist if not handled carefully:
- Misuse can lead to legal issues
- Poor configuration may expose sensitive data
- Ethical boundaries must always remain clear
- Requires technical understanding for safe usage
Conclusion
Zphisher serves as a valuable learning tool within cybersecurity when used responsibly. Its purpose lies in education, awareness, and authorized testing, not exploitation. By focusing on ethical practices, users can gain deep insights into phishing techniques while strengthening defense strategies against real-world threats.
